This is one of several blogs about the vendor presentations during Network Field Day 19, which took place November 7-9, 2018. This blog contains a summary of the vendor presentations and any related comments or opinions I might have (I’ll share at least some of them).
If this blog motivates you to a greater interest in what the vendor had to say, you can find the cleaned up streaming video of their presentations at the Tech Field Day YouTube channel, specifically the NFD19 playlist, or by clicking on the vendor’s logo on the main #NFD19 web page (linked above).
Cisco Secures SD-WAN!
The bulk of the Cisco #NFD19 presentations covered SD-WAN. At the end, there was a presentation about the new Catalyst 9800 physical / virtual Wireless Controller (WLC).
The big (BIG!) news item is the inclusion of firewall and other security features into the Viptela SD-WAN offerings, both on Viptela hardware and the SD-WAN IOS-XE image for ISR/ASR hardware.
That’s a major move, opening up new design alternatives, and potentially competing aggressively with limited SD-WAN device security features in many competitors’ offerings.
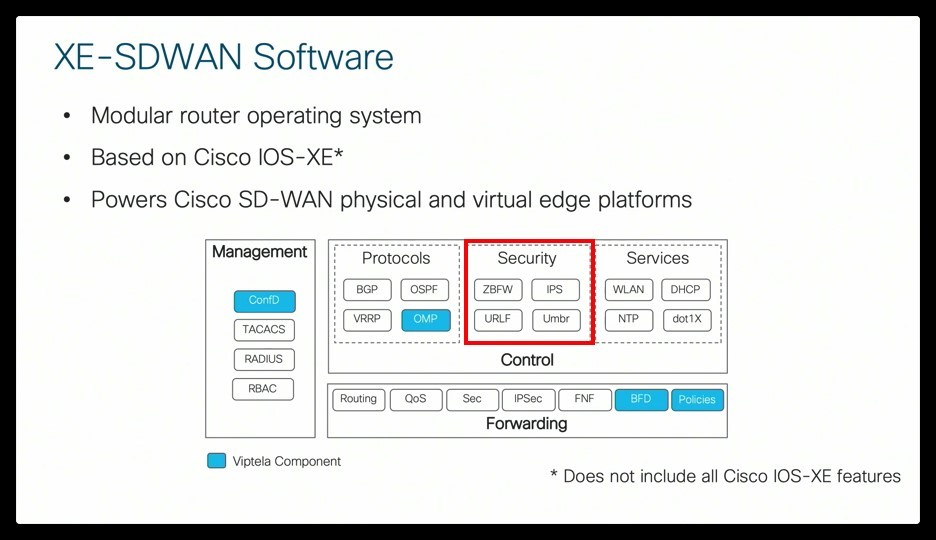
The following graphic pretty much summarizes what’s new for SD-WAN (red rectangle):
Specifically: Zone-Based firewall, URL filtering, IPS, and Umbrella integration. All front-ended by the GUI.
This opens the door to more SD-WAN design / topology options. Specifically, straight to cloud / Internet / SaaS versus regionalized or centralized security stack. It also ties together edge Security and Network Ops in one platform.
Cloud OnRamp
One other feature announced was Cloud OnRamp. Cisco has partnered with Office 365 to find the nearest entry point (in fact, two, for failover) to Microsoft’s global backbone, to reduce latency compared to datacenter backhaul. Microsoft has apparently guaranteed that internal to their backbone they will minimize latency in accessing the various O365 components. Cisco is working to optimize regional access to other cloud providers.
Migrating to Viptela IOS-XE on Routers
Concerning running Viptela on the ISR or ASR router hardware – also discussed – I can’t help but to think of this as the “Viptela on IOS-XE code brain transplant for the ISR/ASR”. I hope you like vivid analogies! The Viptela code is tied to the GUI, so not all prior router features can carry over at present, e.g. EIGRP. That’s a trade-off choice right now: convenience and features of SD-WAN versus whatever you’ve got the router doing right now.
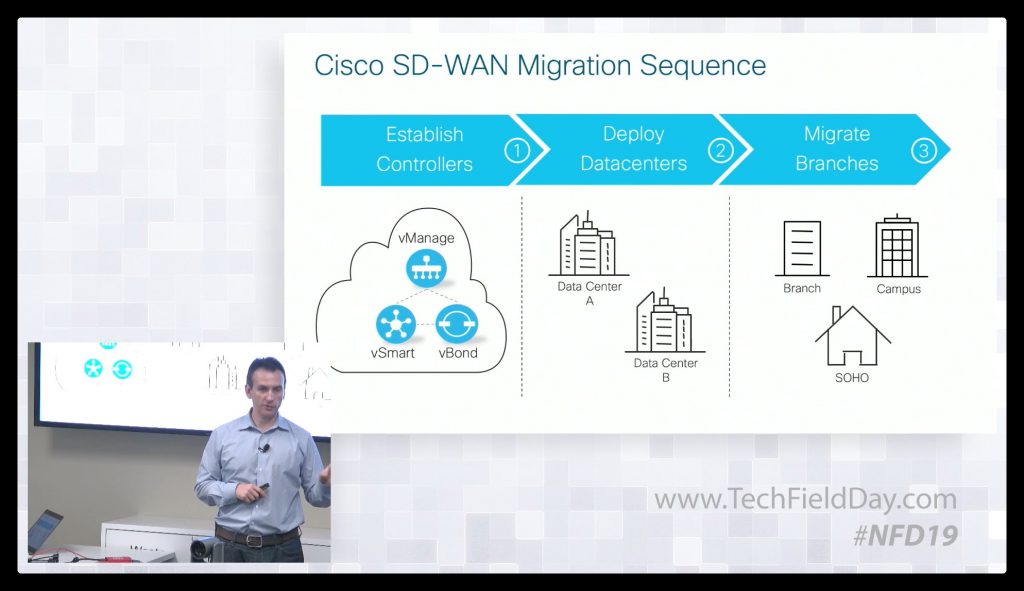
The “Cisco SD-WAN on Cisco Routers” presentation went into migration to the SD-WAN code. The process was described as roughly equivalent to upgrading router code. There is a configuration migration tool which flags incompatible lines and features. When you manually resolve the offending lines, you can cut and paste into vManage. Work is in progress on a more direct process. Cisco has (separately) posted a 30-minute video on the process.
And: The New WLC Line
Concerning the new 9800 series WLC, it is IOS-XE based, controlled by DNA Center (plus RESTful API, etc.). It can run on high performance appliances, in Catalyst 9K switches, or as a virtual appliance, including in the cloud. Performance specs are available for the various options. The new WLC includes automation features to ease hitless WLC or AP upgrades (shift WLAN clients off an AP to a neighbor, or shift the AP to the spare WLC, etc. — beats doing it manually!). See the NFD19 video for more details.
Comments
Comments are welcome, both in agreement or constructive disagreement about the above. I enjoy hearing from readers and carrying on deeper discussion via comments. Thanks in advance!
—————-
Hashtags: #CiscoChampion #TheNetCraftsmenWay #Cisco #SDWAN #NFD19
Twitter: @pjwelcher
NetCraftsmen Services
Did you know that NetCraftsmen does network /datacenter / security / collaboration design / design review? Or that we have deep UC&C experts on staff, including @ucguerilla? For more information, contact us at [email protected].