The easiest way to record a greeting on a call handler in Cisco Unity Connection is to use the Greetings Administrator, but access to it requires some setup. One thing that’s always bugged me is that whenever anyone writes about configuring access to a Greetings Administrator, they always seem to add a call Routing Rule. I’ll admit, my experience with Routing Rules has shown me that they have very sharp teeth and want to attack me.
Typical Routing Rule
I’m much better than I used to be at avoiding death by algorithmic behavior, but I’d still rather steer away from messing with Routing Rules. I know I’m not alone in this, so I’m sharing a less hair-raising method for configuring access to the Greetings Administrator. The secret is to let a Call Handler do most of the work.
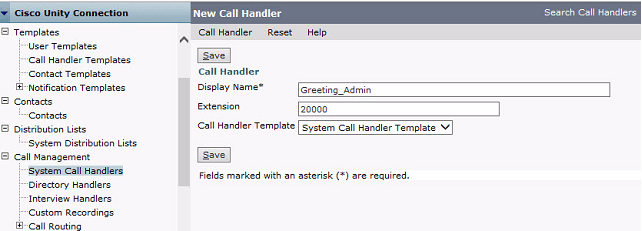
First, I’ll create the Call Handler in Unity Connection by navigating to Call Management > System Call Handlers and adding a new handler with an appropriate name as well as the extension number that people will dial to reach it. Then I’ll click Save.
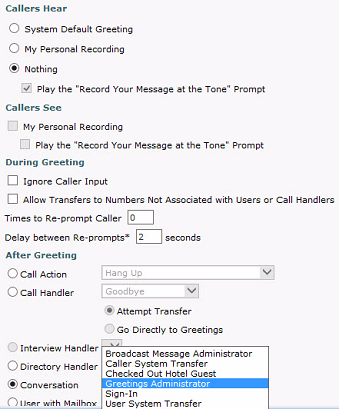
Next, I’ll navigate to Edit > Greetings and select the link for the Standard Greeting. Within the configuration window for the greeting I’ll select the radio button for Nothing in the section marked, “Callers Hear,” and in the After Greeting section I’ll select the Conversation button and – here’s the magic – select Greetings Administrator from the drop-down. Then I’ll save my work.
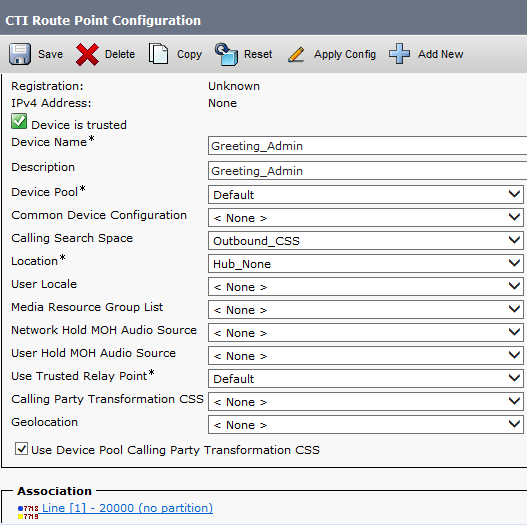
That’s everything required for Unity Connection. However, when one dials the extension it still has to be routed from CUCM to the voicemail cluster. To do this, I usually create a CTI Route Point. In CUCM, I’ll navigate to Device > CTI Route Point and add a new one. The route point is given an appropriate name and Calling Search Space. The Line [1] directory number for the route point is the same as the extension configured on the Call Handler.
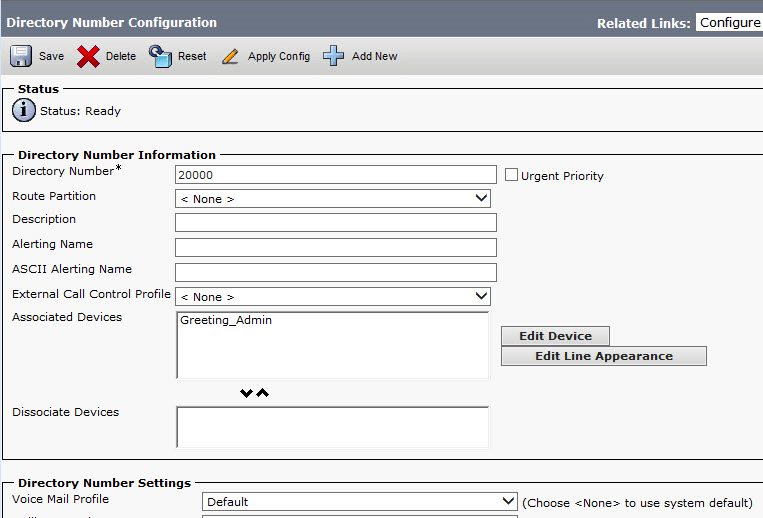
Within the line I’ll configure the Voice Mail Profile so it points to the correct Unity Connection cluster.
And I’ll put a check in the box that automatically forwards all calls to voice mail.
That’s it. Assuming everything tests correctly, people should be able to call the Greetings Administrator extension, and – assuming they have rights to additional call handlers – they should be able to record whatever greetings are required.
Comments
Comments are welcome, both in agreement or constructive disagreement about the above. I enjoy hearing from readers and carrying on deeper discussion via comments. Thanks in advance!