Hello again! This blog will briefly cover the presentations by KEMP Technologies at #NFD16. If you’re interested and want more detail, watch the streaming video recordings of the KEMP Technologies presentations.
Who Is KEMP?
Yes, that was definitely the first question, since I’d never heard of KEMP Technologies before. The KEMP Technologies (“KEMP” for short) logo says “Application Delivery.” OK, that’s short and to the point.
The products menu on their website says: load balancers (hardware, virtual, cloud, bare metal, multi-tenant) and also mentions KEMP 360 (management/control).
KEMP Solutions include load balancing, GSLB (DNS-based LB), WAF (web application firewall), edge security, reverse proxy (encryption offload, caching, compression).
To sum up: KEMP makes SLBs with optional features. That somewhat aligns with a Greg Ferro Packet Pusher blog (albeit in a Riverbed/SD-WAN setting. I’ll paraphrase it as being about WAN edge and applications — I see it to some extent as Network Function Virtualization (NFV) stacking. One might extend that to the SLB market: It’s about cutting the box count and getting more functionality in the WAN or internet edge.
The virtual SLB aspect is interesting, and aligned with what other vendors are doing. If you want familiar features common across physical and cloud infrastructure, having both approaches from a vendor could be helpful. In one management platform, more helpful. I will note that I’ve always been more comfortable with SLB appliances than with server-based load balancing (i.e., non-virtualized appliance forms of load balancing). For cloud and web-scale out applications, there may be benefits to one or the other approach, depending on the application structure.
What Else?
The short list of takeaway items from the KEMP presentations:
- KEMP makes an SLB in physical, virtual, and cloud formats; they also do clustering.
- KEMP says they are doing well in Azure.
- Virtual appliances keep you from being tied to a particular cloud platform.
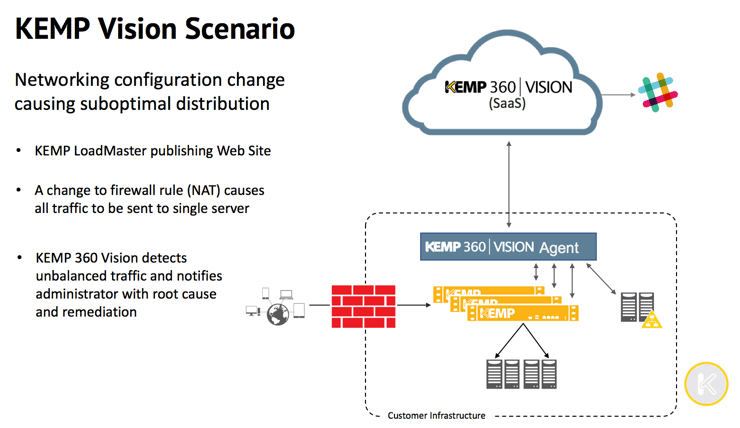
- KEMP’s 360 Central manages physical and virtual SLBs, including other vendors’ products to some degree, does some traffic reporting, etc. KEMP 360 Vision provides traffic visibility and alerting, via email, Slack, Twitter, or other methods.
- KEMP 360 has “VS Motion.”
- KEMP has a new metered “MELA” licensing model that is based on peak loading of traffic. This is claimed to scale well across many small virtual appliances or fewer big/physical ones, although the NFD group had some questions about failover situations, among others (i.e., one should probably game various scenarios if contemplating the KEMP licensing).
- KEMP supports automation via PowerShell (which, by the way, is available on increasing numbers of non-Microsoft platforms).
Caveat: The above is for some value of “manage,” presumably some common denominator stuff. I’d expect at least VIPs and ports and server pools.
The VS Motion is supposed to sound like vMotion, I guess. It seems to be automation of shifting the VIP from one set of SLBs to another. It does not support pre-validation of moves, e.g. if you move the VIP to SLB pair B, do they have the necessary front- and back-end connectivity (think firewalls and ACLs)? One can hope that KEMP might engineer support for that into its SLBs. Doing the necessary checking for the competition might be a bit harder.
Summary
KEMP presented some interesting ideas. I’m a believer in hands-on experience and field testing. I have no data either way about the KEMP products. My intent for this blog is to inform you about KEMP, so you can decide your own level of interest.
References
Chris Marget had some interesting comments in KEMP Presented Some Interesting Features at NFD16.
Comments
Comments are welcome, both in agreement or constructive disagreement about the above. I enjoy hearing from readers and carrying on deeper discussion via comments. Thanks in advance!


