The 2017 RSA Conference was filled with interesting, inspiring, and informative topics. My limited experience in security allowed me to come in with an open mind; I was willing to dive right into the deep end.
Knowing the fragmented and compartmentalized nature of this industry, my approach to the conference was simple: Take it all in. Determine the security strategies that resonated with me the most. I didn’t have one specific areas of focus; I truly sought knowledge about every aspect of security.
Here’s a recap of my experience at the conference.
Monday Feb. 13, 2017:
On day one of the RSA Conference, I attended the Cloud Security Alliance Summit, which featured speakers from a variety of companies including Microsoft, Cryptzone, and Centrify, to name a few. There were a ton of great talking points around the cloud, DevSecOps and cyber security. One phrase in particular captivated me and captured the overall mood of the event: “Take advantage of the attention to do it right,” said Jason Garbis, vice president of products, Cryptzone.
I immediately understood the requirement: In an industry that is completely fragmented, we need to come together to make security empowering. Thomas Kemp from Centrify stated that we have seen a 2.1 trillion-dollar cost associated with breaches. And that makes sense; we have seen some historic attacks in recent years:
- DYN DNS Attack
- Yahoo Hack (Impacted over 1B users)
- Ransomware LG TV Attack
Looking at it from an outside perspective, we need to massively rethink security. This seemed to be the tone throughout the entire conference. Keeping with the theme of security, one cloud security product in particular caught my attention: The Software Defined Perimeter by Cryptzone. This new network security model focuses on:
- Hiding servers
- Dynamically creating secure connections
- Individualizing users
Tuesday, Feb. 14, 2017:
Day two of the RSA Conference started with keynote speakers. The first speaker, from McAfee, started with a discussion around cloud, but quickly shifted to IoT (Internet of Things) as a new attack service.
“Who takes the home into consideration when designing cybersecurity?” the speaker asked. He said we must understand that freedom does create more susceptibilities, and we need to make sure that IoT does not become the “Internet of Terrorism.” His last point really caught my attention: “The target has now become the weapon.” In other words, our own data is now being weaponized to be used against us.
The second part of the keynote was a cryptographers panel. The takeaway that stayed with me was the phrase, “In order to solve the internet, we must kill it” — meaning that we have lost control of our personal data and must be prepared to expand on the regulation of the internet.
At the expo, there was one company in particular that stood out: Bitglass, a complete CASB solution. Bitglass prides itself on total data protection:
Cloud security
- Dissect your organization’s cloud usage
- Focus on securing data at the source
- Access control available at a very granular level
Mobile security
- Help protect staff privacy
- Police the mobile data and build violation policies
- Manage devices without agents or MDM
Breach discovery
- Quick discovery for limited impact
- Precise threat detection and auto-prioritization
I received a live demo of the product, and found the user interface to be intuitive and robust.
Wednesday, Feb. 15, 2017:
Day three of the conference begin with a security workshop on virtualization and software-defined architecture, hosted by Dave Shackleford from the SANS Institute. Dave began with an overview on technologies such as NFV, SDN, and DevSecOps, then jumped into the new “security stack,” which includes:
- Application logic + presentation
- Operating systems
- Data
- Network
- Hypervisor
Next, I attended a peer-to-peer session that brought organizations together to talk about cloud migration strategies, which focused on hybrid and multi-cloud architectures. Most of the conversation centered on:
- Data security
- Key management (HSM requirement)
- Identity as a service
- Virtual appliance for key management
- Log/monitor/audit
- Logging collection and strategies should be outlined before migrating to the Cloud
- Incident Response from your cloud provider
- Audit trails
- CASB
I then attended a mini session on DDoS attacks presented by Neuster, which explored denial of service attacks of the future (IoT botnets and soda machines impacting universities were just a few examples). Neuster’s approach to preparing for the future is through scale. They are currently working on a 10-Terabit scrubber network as their short-term solution. Long-term, they believe we need to strategize using software. They would like the industry to think of software as art and play close attention the IoT boom.
Thursday, Feb. 16, 2017:
My last day at the conference opened with DevSecOps. The session explored developer security adoption, and I noticed that there seems to be a disconnect between developers and their security teams. A few key points from the session:
- Security team members that do not add value to the developmental process are usually not included in meetings
- Find ways to encourage developers to adopt security
- Don’t put focus on the term DevSecOps; “just do DevOps securely”
- Transition developers to security expertise because they know code
After attending morning keynotes, I had a two-part session on transforming security. Part one focused on cloud and virtualization. Currently, the application is the network, and we must find better security practices to mitigate risk. The presenter, Tom Corn from VMWare, advised us to think of our critical applications as our baby — a memorable analogy.
During our session, we focused on moving away from traditional perimeter security such as multiple firewalls, which only add complexity and do not contain lateral movement. Tom focused on shrinking the grey area of security; we need to understand more black and white. We discussed a couple of ways to accomplish this:
- Go back to a least privilege design, not just blocking
- Monitor, detect and respond
- Don’t focus on malicious behavior
- Focus on good intended behavior: Create a better signal-to-noise ratio
- Think of virtualization as an abstraction layer
- Micro-segmentation: Create isolated boundaries and create controls around that boundary
Part two of the session focused on users and their devices, including the following key items:
- Build a policy framework for users
- Conditional access
- Limited access
- Prevent ransomware
- User evaluation
- Host-based security
- Limit lateral movement
- Solve complex problems
- Patch and secure users
- Adopt “Zero Trust”
The session ended with a quote from MIT Professor Jerome Saltzer: “Every program and every privileged user of the system should operate using the least amount of privilege necessary to complete the job.”
Overall, I was impressed by the RSA Conference. Even as a new kid on the block, I found myself immersed in discussions with different IT security professionals. However, there does seem to be a sense of compartmentalization among those in this industry. Despite talks about coming together to accomplish a common mission, I did not see that messaging amongst vendors at this event. At least there is one vendor that has the right message:
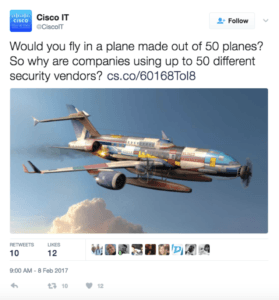
We will see how they build on this strategy.
