This blog is a small follow-up to the Neat Cisco Nexus Features You Might Have Missed blog.
Some Cisco folks pointed me to the “Catena” feature, implemented in some Cisco Nexus 9K and in the Nexus 7K models. Catena is Latin for “chain”.
From one point of view, Catena is locally-configured hybrid OpenFlow. That is, locally-configured specification of over-ride behavior forwarding (or dropping) based on flow specifications.
What Is Catena
Catena lets you build service chains for services from devices that connect to a single datacenter switch. That is, you can force selected traffic through external devices 1, 2, 3, etc. For example; firewall, IPS, IPsec MITM box, whatever.
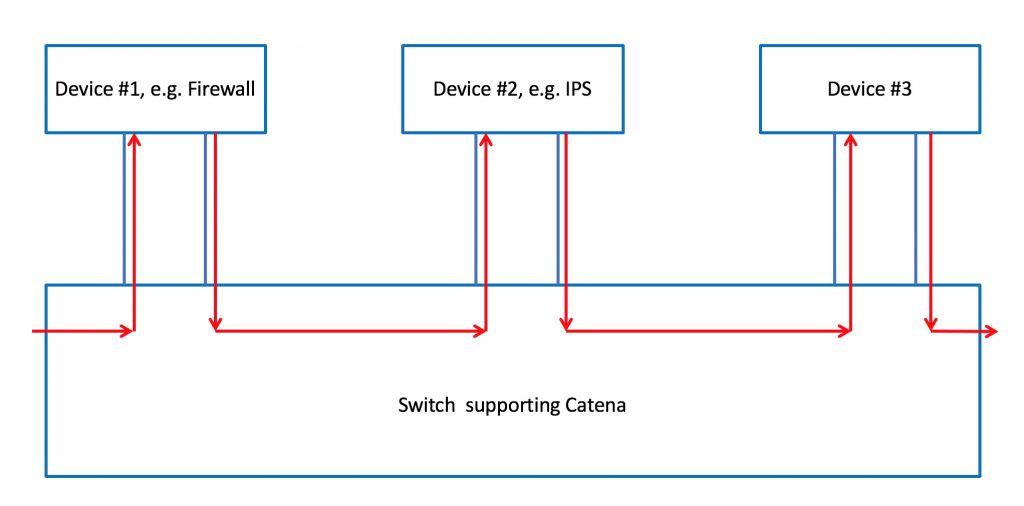
Here’s a diagram showing what you can do with Catena:
This to a degree generalizes the ITD topic discussed in my prior blog (link above). It is done by modifying TCAM, so you get full performance. Catena uses the notion of device groups: it load balances across devices within configured device groups.
I’ll note that Catena has “transparent” (L2) and routed modes. For more, I’ll Reference the Fine Manual (RTFM) — Nexus 9K version (or see also the Nexus 7K link below).
My Reaction
If you need to selectively forward to or bypass certain devices, Catena could be very handy.
I do need to note that selective forwarding based on more than destination address does complicate things. Factoring in behavior based on source address or source / destination port means more forwarding equivalence classes of traffic, each behaving in their own way. More to understand! This is not necessarily good or bad, it is more to note that using a feature like this adds complexity, and you need to think about managing that complexity.
My Beer Principle likely applies: one beer good, many beers equals headache. Do too much Catena, and you may develop a headache?
References
- https://blogs.cisco.com/datacenter/catena-a-disruptive-innovation
- https://blogs.cisco.com/datacenter/catena-and-other-innovations
- 2018 CiscoLive presentation
- 2017 CiscoLive presentation
- https://www.networkcomputing.com/data-centers/best-interop-itx-2017-winners-revealed/274104047
- https://www.cisco.com/c/en/us/td/docs/switches/datacenter/nexus7000/sw/catena/config/cisco_nexus7000_catena_config_guide_8x/configuring_catena.html
Comments
Comments are welcome, both in agreement or constructive disagreement about the above. I enjoy hearing from readers and carrying on deeper discussion via comments. Thanks in advance!
—————-
Hashtags: #CiscoChampion #TheNetCraftsmenWay #CiscoCatena #CiscoNexus #DataCenter
Twitter: @pjwelcher
NetCraftsmen Services
Did you know that NetCraftsmen does network /datacenter / security / collaboration design / design review? Or that we have deep UC&C experts on staff, including @ucguerilla? For more information, contact us at [email protected].


