When a single router serves two buildings how can you configure it to support emergency services?
Configuring SRST support for 2 sites
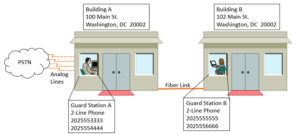
Let’s say there are two buildings on a system that are physically right next to each other. Building A is at 100 Main St. in Washington, DC and Building B is a 102 Main St. The buildings are so close that they are connected with a strand of fiber that runs under an alley. Because there aren’t that many people in each building, the customer figures that they can get away with a single router that can act as both a WAN edge device, as well as a voice gateway that connects to a dozen analog lines.
During normal operation, when a call comes into the office, it hits the analog port, and a phone number is assigned to it using a PLAR statement.
PLAR, by the way, is “Private Line Automatic Ringdown” and in the case of an analog line attached to a voice gateway it tells the gateway that when a call comes in on that line it’s supposed to be directed to a phone with the extension mentioned in the PLAR statement.
When a call leaves the office there are incoming dial-peers on the gateway that add prefixes to the called numbers so that they will hit specific outbound dial-peers. Those outbound dial-peers direct the calls through the analog lines that are associated to the number on each phone. The reason for this isn’t just caller-ID. The lines are also associated to a specific building. Even though the lines all terminate at Building A, the PSTN (local phone company) recognizes that half are associated to that building, but the other half are associated to Building B. This is so emergency responders will show up at the correct location if someone calls 911.
Problem. What happens when the day isn’t so “sunny?” What if the WAN dies, the phones cannot reach the call control server, and they go into Survivable Remote Site Telephony (SRST) mode which will cause the local gateway to act as the call controller? As has been stated in a previous blog post (https://netcraftsmen.com/configuring-srst-on-cme), when a phone goes into SRST there is a dial-peer created on-the-fly by the router that is used as both an outbound dial-peer when the call is going from the gateway to the internal phone, as well as an inbound dial-peer when the call is coming from the internal phone to the gateway. That means that the manually configured incoming dial-peers no longer come into play during SRST.
So, in a WAN-down situation, how would the gateway identify a call coming from a specific caller and send that call to the correct dial-peer and the correct analog port going to the PSTN? The answer is by identifying the IP address of the caller.
This is something that is poorly documented, and where there is information it leads one to believe that it only works in an environment using Cisco CallManager Express (CME) for SRST. That’s not the case. Beginning with the Cisco 12.4(20)T IOS, it’s possible to identify the source IP of a phone and send the call out the appropriate port. The configuration look something like this:
voice emergency response location 1
subnet 1 192.168.0.0 255.255.255.240
!
voice emergency response location 2
subnet 1 192.168.1.0 255.255.255.240
!
voice emergency response zone 1
location 1 priority 1
!
voice emergency response zone 2
location 2 priority 1
!
dial-peer voice 1 pots
port 0/0/0
description Outbound 911 for number 555-1111
destination-pattern 911
emergency response zone 1
!
dial-peer voice 2 pots
port 0/0/1
description Outbound 911 for number 555-2222
destination-pattern 911
emergency response zone 2
Note that the emergency response zones can have only 2 subnets in them, so if the sites are large enough, the networks listed might have to be supernetted.
This 2-subnet limit is kind of a bummer if the building is large enough to have several floors with different subnets on them and you want to try to pinpoint the location of the caller. In a case like that you’ll probably have to make other arrangements like having an on-site call control server and an on-site emergency responder server that will send calls with appropriate location information.
Also, if the ports are attached to PRI lines (or even a single ISDN line) instead of analog lines 911 calls will only work if there is an ELIN (callback number) and an ALI (location address) pinned to the call. Otherwise the call will be rejected by the router (there won’t even be an attempt to send it to the PRI). The ELIN, therefore, may have to be a single number of someone who is always in the building during business hours, or a pilot number that leads to a hunt group that rings several phones. The ALI will be the address of the appropriate building.
If an ELIN and an ALI are added, the location will look something like this:
voice emergency response location 1
subnet 1 192.168.0.0 255.255.255.240
elin 1 2025551111
address 100, Main St., Washington, DC, 20002
name Floor 1
!
voice emergency response location 2
subnet 1 192.168.1.0 255.255.255.240
elin 1 2025552222
address 102, Main St., Washington, DC, 20002
name Floor 1
The hunt groups might look like this:
voice hunt-group 1 parallel
list 2025553333,2025554444
timeout 20
pilot 2025551111
!
voice hunt-group 2 parallel
list 2025555555,2025556666
timeout 20
pilot 2025552222