One of my customers has been converting his core 6500 switches over to Nexus 7700 switches. In the first project phase, the plan was to try to just move what was currently configured on the old cores over to the new core devices. Since this was mainly a switched environment, this seemed like a reasonable plan. He was planning to move one site at a time.
On the second morning of one of the maintenance windows to the new devices, we ran into an issue. When we reconnected one of the last access switches planned for the morning, the link came up, the port-channel came up, but we lost connectivity with the devices on the access switch and the access switch itself.
We checked the configs on the new core switch; the configuration looked fine:
This closely matched the old 6500 configuration:
The differences make sense. The NX-OS default for the channel-group 3 interface command is mode on. The default trunk encapsulation for NX-OS is 802.1q.
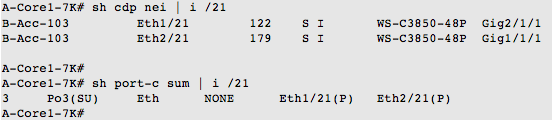
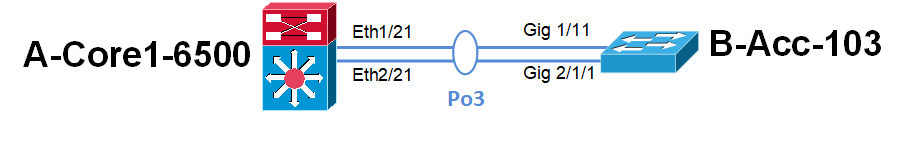
We noticed that the two links were up, we were forming neighbors, and were up in a port-channel:
We reconnected the link back to the 6500, and regained connectivity.
Since we had other devices to migrate, we noted this issue, and moved on to the other connections planned for that maintenance window.
Finding the Issue
Later that morning, we looked at the remote switch after it was reconnected to the 6500 switch.
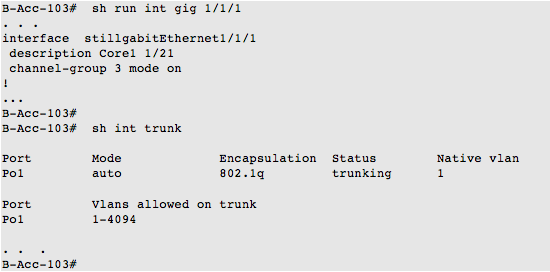
We noticed that Gig 1/1/1 had no configured trunk commands, but was still up in trunk mode. The customer mentioned that since the 3850s and newer switches seemed to just come up as trunks, they had not always configured a switchport mode trunk on the uplinks.
After a bit of review, we determined that the default switchport mode for newer Cisco switch interfaces is dynamic auto, which matches the mode auto we saw in the show interface trunk command. The configuration guide states “The interface becomes a trunk interface if the neighboring interface is set to trunk or desirable mode.”
However, the 3850 interfaces also did not become trunks when connected to the Nexus switch that was configured with the switchport mode trunk command.
Reviewing other documentation, we noticed:
- On a 6500: switchport mode trunk — Puts the LAN port into permanent trunking mode and negotiates to convert the link into a trunk link. The LAN port becomes a trunk port even if the neighboring port does not agree to the change.
- On a 3850: switchport mode trunk — Puts the interface into permanent trunking mode and negotiates to convert the neighboring link into a trunk link. The interface becomes a trunk interface even if the neighboring interface is not a trunk interface.
The 3850s run dynamic trunk protocol (DTP) by default. The 3850 configuration guide assumes that the remote switch is also running DTP, which 6500s do by default.
- On a N7K: switchport mode trunk — Specifies the trunking VLAN interface in Layer 2. A trunk port can carry traffic in one or more VLANs (based on the trunk allowed VLAN list configuration) on the same physical link.
OK, this identifies the root issue. The NX-OS documentation does not mention negotiating with the remote site to do anything. This makes sense when you know/remember that DTP is NOT supported on NX-OS. The 3850’s port channel came up as an access port in the default VLAN 1.
This access port was not a match for the trunk configuration on the NX-OS switch. No traffic was configured to use the default VLAN 1, so A-Core1-7K lost connectivity to the other VLANs on B-Acc-103. We needed to have a matching trunk on the remote access switch side.
Solution
We added the switchport mode trunk command to B-Acc-103 while it was connected the 6500; it stayed up as a trunk. We switched the link back to the N7K, and the trunk stayed up. The problem was resolved.
The default behavior of switches sometimes changes. This can be an issue when you are relying on defaults.