Business leaders can benefit from understanding how network monitoring can improve their business.
“If you can’t measure it, you can’t manage it.” — Peter Drucker
Image Source: https://s-media-cache-ak0.pinimg.com/736x/46/2a/3d/462a3d960509c25f7183ff6defce858e.jpg
Peter Drucker’s quote is one of the most common business management axioms. Business leaders tend to focus on high-level measurements and management, so network management is simply too down in the weeds for most leaders. Managing the network typically falls to mid-level managers, who have to juggle business requirements and budgets. A gap then exists between network operations and what the business leaders think is happening.
Network infrastructure is similar to other physical infrastructure, such as conveyor belts, sorters, plumbing, pumps, and assembly lines. None of this infrastructure can be ignored without risk to the business.
A Failure to Measure
Our network assessments often find that organizations don’t allocate funds or staff resources to adequately monitor their network infrastructure. For example, key WAN interfaces will be monitored, but data center interfaces will be ignored. “It’s too expensive” is a common response. If you must make compromises, don’t do it on the business-critical infrastructure.
A related problem is the lack of staff resources to run the network monitoring systems. Network monitoring generates a large volume of data, of which only a very small percentage contains valuable information. The network management systems must help the staff track key metrics and identify potential problems.
Apply the Implementation Maturity Model
The Implementation Maturity Model can give you an idea of the maturity of your network monitoring systems. At what point is the network infrastructure implementation mature (Initial, Repeatable, Defined, Managed, or Optimizing)? The upper IMM levels are critical to a smoothly operating network, whose operation must be predictable to allow the detection of anomalies.
Do You Have the Right Tools?
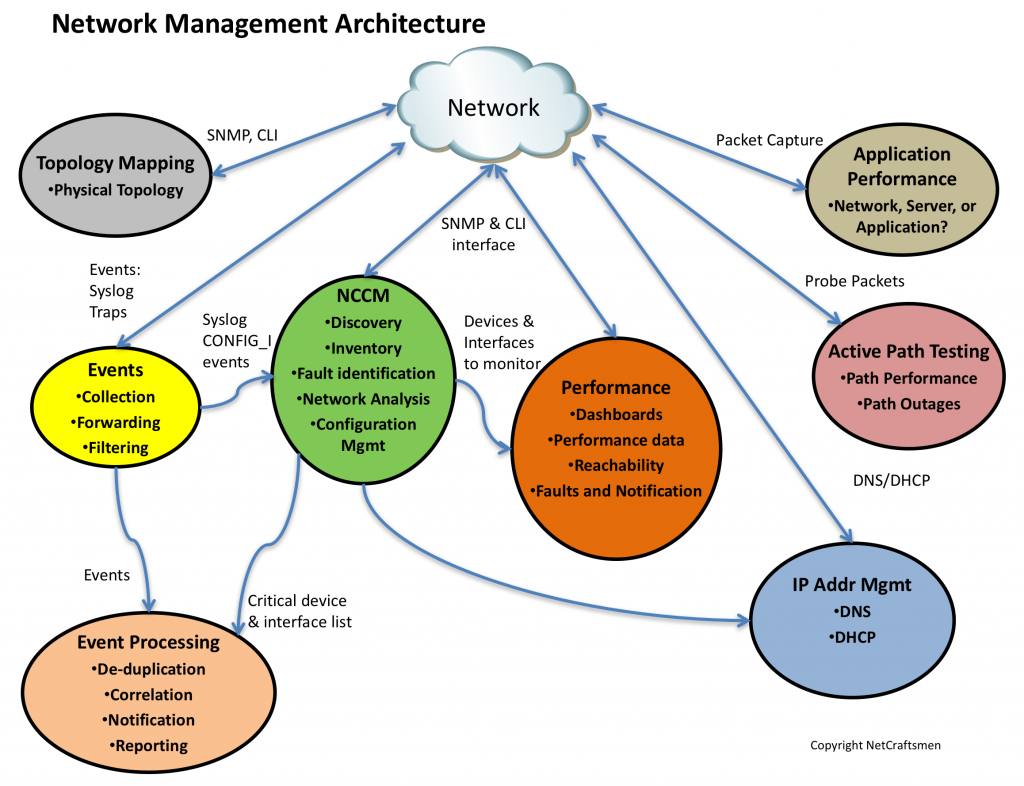
What tools do you need? We’ve developed a network management architecture that identifies the key components. Map your tool set to the different functions to identify duplication and holes.
- Event Management — syslog, SNMP traps, and application error alerts.
- Network Change and Configuration Management — verifying configurations and configuration automation.
- Performance Monitoring — identifies interface errors, drops, and device problems.
- IP Address Management — tracks IP address allocations and provide DHCP/DNS services.
- Active Path Testing — end-to-end path testing with synthetic or real transactions.
- Application Performance — resolves problems to applications or network.
- Topology Mapping — tracking physical and logical network connections.
Services
Outsourcing the network management functions is an alternative to assembling your own tool suite. This may be a less expensive approach. We offer Craftsmen Assurance® as a service to organizations who wish to switch to an OpEx financial model and want to rely on our expertise.
Wrapping It Up
There are three steps to managing the network. The level of effort required for each step depends greatly on your current network management architecture. The exact tools will depend on the network size and staff capabilities.
- Monitor the critical network infrastructure.
- Use the IMM to build repeatable processes and consistent network topologies.
- Implement the full tool suite or consider outsourcing.
If you’re not sure where to start, contact us and we can arrange for a network assessment, including network management review.
—————-
Hashtags: #CiscoChampion #TheNetCraftsmenWay #NetworkMonitoring #NetworkManagement
